ntp-keygen - generate public and private keys
Last update: March 23, 2023 21:05 UTC (6ad51a76f)
from Alice’s Adventures in Wonderland, Lewis Carroll
Alice holds the key.
Table of Contents
Synopsis
ntp-keygen [ -deGHIMPT ] [ -b modulus ] [ -c [ RSA-MD2 | RSA-MD5 | RSA-SHA | RSA-SHA1 | RSA-MDC2 | RSA-RIPEMD160 | DSA-SHA | DSA-SHA1 ] ] [ -C cipher ] [-i group ] [ -l days] [ -m modulus ] [ -p passwd1 ] [ -q passwd2 ] [ -S [ RSA | DSA ] ] [ -s host ] [ -V nkeys ]
Description
This program generates cryptographic data files used by the NTPv4 authentication and identity schemes. It can generate message digest keys used in symmetric key cryptography and, if the OpenSSL software library has been installed, it can generate host keys, sign keys, certificates, and identity keys and parameters used by the Autokey public key cryptography. The message digest keys file is generated in a format compatible with NTPv3. All other files are in PEM-encoded printable ASCII format so they can be embedded as MIME attachments in mail to other sites.
When used to generate message digest keys, the program produces a file containing ten pseudo-random printable ASCII strings suitable for the MD5 message digest algorithm included in the distribution. If the OpenSSL library is installed, it produces an additional ten hex-encoded random bit strings suitable for the SHA1, AES-128 CMAC, and other message digest algorithms. The message digest keys file must be distributed and stored using secure means beyond the scope of NTP itself. Besides the keys used for ordinary NTP associations, additional keys can be defined as passwords for the ntpq and ntpdc utility programs.
The remaining generated files are compatible with other OpenSSL applications and other Public Key Infrastructure (PKI) resources. Certificates generated by this program are compatible with extant industry practice, although some users might find the interpretation of X509v3 extension fields somewhat liberal. However, the identity keys are probably not compatible with anything other than Autokey.
Some files used by this program are encrypted using a private password. The -p option specifies the password for local encrypted files and the -q option the password for encrypted files sent to remote sites. If no password is specified, the host name returned by the Unix gethostname() function, normally the DNS name of the host, is used.
The pw option of the crypto configuration command specifies the read password for previously encrypted local files. This must match the local password used by this program. If not specified, the host name is used. Thus, if files are generated by this program without password, they can be read back by ntpd without password, but only on the same host.
Normally, encrypted files for each host are generated by that host and used only by that host, although exceptions exist as noted later on this page. The symmetric keys file, normally called ntp.keys, is usually installed in /etc. Other files and links are usually installed in /usr/local/etc, which is normally in a shared filesystem in NFS-mounted networks and cannot be changed by shared clients. The location of the keys directory can be changed by the keysdir configuration command in such cases. Normally, this is in /etc.
This program directs commentary and error messages to the standard error stream stderr and remote files to the standard output stream stdout where they can be piped to other applications or redirected to files. The names used for generated files and links all begin with the string ntpkey and include the file type, generating host and filestamp, as described in the Cryptographic Data Files section.
Running the Program
To test and gain experience with Autokey concepts, log in as root and change to the keys directory, usually /usr/local/etc. When run for the first time, or if all files with names beginning ntpkey have been removed, use the ntp-keygen command without arguments to generate a default RSA host key and matching RSA-MD5 certificate with expiration date one year hence. If run again without options, the program uses the existing keys and parameters and generates only a new certificate with new expiration date one year hence.
Run the command on as many hosts as necessary. Designate one of them as the trusted host (TH) using ntp-keygen with the -T option and configure it to synchronize from reliable Internet servers. Then configure the other hosts to synchronize to the TH directly or indirectly. A certificate trail is created when Autokey asks the immediately ascendant host towards the TH to sign its certificate, which is then provided to the immediately descendant host on request. All group hosts should have acyclic certificate trails ending on the TH.
The host key is used to encrypt the cookie when required and so must be RSA type. By default, the host key is also the sign key used to encrypt signatures. A different sign key can be assigned using the -S option and this can be either RSA or DSA type. By default, the signature message digest type is MD5, but any combination of sign key type and message digest type supported by the OpenSSL library can be specified using the -c option.
The rules say cryptographic media should be generated with proventic filestamps, which means the host should already be synchronized before this program is run. This of course creates a chicken-and-egg problem when the host is started for the first time. Accordingly, the host time should be set by some other means, such as eyeball-and-wristwatch, at least so that the certificate lifetime is within the current year. After that and when the host is synchronized to a proventic source, the certificate should be re-generated.
Additional information on trusted groups and identity schemes is on the Autokey Public-Key Authentication page.
Command Line Options
-b modulus- Set the modulus for generating identity keys to modulus bits. The modulus defaults to 512, but can be set from 512 (64 octets) to 2048 (256 octets). Use the larger moduli with caution, as this can consume considerable computing resources and increases the size of authenticated packets.
-c [ RSA-MD2 | RSA-MD5 | RSA-SHA | RSA-SHA1 | RSA-MDC2 | RSA-RIPEMD160 | DSA-SHA | DSA-SHA1 ]- Select certificate digital signature and message digest scheme. Note that RSA schemes must be used with an RSA sign key and DSA schemes must be used with a DSA sign key. The default without this option is
RSA-MD5. If compatibility with FIPS 140-2 is required, either the DSA-SHA or DSA-SHA1 scheme must be used.
-C cipher- Select the OpenSSL cipher to use for password-protected keys. The
openssl -h command provided with OpenSSL displays available ciphers. The default without this option is des-ede3-cbc.
-d- Enable debugging. This option displays the cryptographic data produced for eye-friendly billboards.
-e- Extract the IFF or GQ public parameters from the
IFFkey or GQkey keys file previously specified. Send the unencrypted data to the standard output stream stdout.
-G- Generate a new encrypted GQ key file for the Guillou-Quisquater (GQ) identity scheme. This option is mutually exclusive with the
-I and -V options.
-H- Generate a new encrypted RSA public/private host key file.
-i group- Set the optional Autokey group name to
group. This is used in the identity scheme parameter file names. In that role, the default is the host name if no group is provided. The group name, if specified using -i or using -s following an @ character, is also used in certificate subject and issuer names in the form host@group and should match the group specified via crypto ident or server ident in ntpd’s configuration file.
-I- Generate a new encrypted IFF key file for the Schnorr (IFF) identity scheme. This option is mutually exclusive with the
-G and -V options.
-l days- Set the lifetime for certificates to
days. The default lifetime is one year (365 d).
-m modulus- Set the modulus for generating files to modulus bits. The modulus defaults to 512, but can be set from 512 (64 octets) to 2048 (256 octets). Use the larger moduli with caution, as this can consume considerable computing resources and increases the size of authenticated packets.
-M
Generate a new keys file containing 10 MD5 keys and 10 SHA keys. An MD5 key is a string of 20 random printable ASCII characters, while a SHA key is a string of 40 random hex digits. The file can be edited using a text editor to change the key type or key content. This option is mutually exclusive with all other options.
-P- Generate a new private certificate used by the PC identity scheme. By default, the program generates public certificates.
Note: the PC identity scheme is not recommended for new installations.
-p passwd- Set the password for reading and writing encrypted files to
passwd. These include the host, sign and identify key files. By default, the password is the string returned by the Unix gethostname() routine.
-q passwd- Set the password for writing encrypted IFF, GQ and MV identity files redirected to
stdout to passwd=. In effect, these files are decrypted with the -p password, then encrypted with the -q password. By default, the password is the string returned by the Unix gethostname() routine.
-S [ RSA | DSA ]- Generate a new encrypted public/private sign key file of the specified type. By default, the sign key is the host key and has the same type. If compatibly with FIPS 140-2 is required, the sign key type must be
DSA.
-s host[@group]- Specify the Autokey host name, where
host is the host name and group is the optional group name. The host name, and if provided, group name are used in host@group form as certificate subject and issuer. Specifying -s @group is allowed, and results in leaving the host name unchanged, as with -i group. The group name, or if no group is provided, the host name are also used in the file names of IFF, GQ, and MV identity scheme parameter files. If host is not specified, the default host name is the string returned by the gethostname() routine.
-T- Generate a trusted certificate. By default, the program generates nontrusted certificates.
-V nkeys- Generate
nkeys encrypted server keys for the Mu-Varadharajan (MV) identity scheme. This option is mutually exclusive with the -I and -G options.
Note: support for this option should be considered a work in progress.
Random Seed File
All cryptographically sound key generation schemes must have means to randomize the entropy seed used to initialize the internal pseudo-random number generator used by the OpenSSL library routines. If a site supports ssh, it is very likely that means to do this are already available. The entropy seed used by the OpenSSL library is contained in a file, usually called .rnd, which must be available when starting the ntp-keygen program or ntpd daemon.
The OpenSSL library looks for the file using the path specified by the RANDFILE environment variable in the user home directory, whether root or some other user. If the RANDFILE environment variable is not present, the library looks for the .rnd file in the user home directory. Since both the ntp-keygen program and ntpd daemon must run as root, the logical place to put this file is in /.rnd or /root/.rnd. If the file is not available or cannot be written, the program exits with a message to the system log.
Cryptographic Data Files
File and link names are in the form ntpkey_key_name.fstamp, where key is the key or parameter type, name is the host or group name and fstamp is the filestamp (NTP seconds) when the file was created. By convention, key names in generated file names include both upper and lower case characters, while key names in generated link names include only lower case characters. The filestamp is not used in generated link names.
The key name is a string defining the cryptographic key type. Key types include public/private keys host and sign, certificate cert and several challenge/response key types. By convention, client files used for challenges have a par subtype, as in the IFF challenge IFFpar, while server files for responses have a key subtype, as in the GQ response GQkey.
All files begin with two nonencrypted lines. The first line contains the file name in the format ntpkey_key_host.fstamp. The second line contains the datestamp in conventional Unix date format. Lines beginning with # are ignored.
The remainder of the file contains cryptographic data encoded first using ASN.1 rules, then encrypted using the DES-CBC algorithm with given password and finally written in PEM-encoded printable ASCII text preceded and followed by MIME content identifier lines.
The format of the symmetric keys file, ordinarily named ntp.keys, is somewhat different than the other files in the interest of backward compatibility. Ordinarily, the file is generated by this program, but it can be constructed and edited using an ordinary text editor.
Figure 1: Typical Symmetric Key File
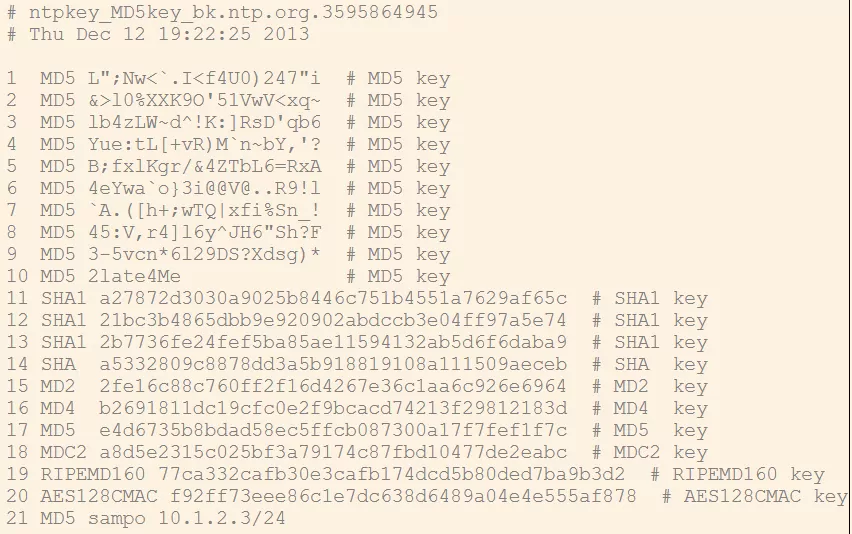
Figure 1 shows a typical symmetric keys file used by the reference implementation. Each line of the file contains three or four fields, first an integer between 1 and 65535, inclusive, representing the key identifier used in the server and peer configuration commands. Second is the key type for the message digest algorithm, which in the absence of the OpenSSL library must be MD5 to designate the MD5 message digest algorithm. If the OpenSSL library is installed, the key type can be any message digest algorithm supported by that library. However, if compatibility with FIPS 140-2 is required, the key type must be either SHA or SHA1. The key type can be changed using an ASCII text editor.
The third field is the key.
An MD5 key consists of a printable ASCII string less than or equal to 16 characters and terminated by whitespace or a # character. An OpenSSL key consists of a hex-encoded ASCII string of 40 characters, which is truncated as necessary.
Note that the keys used by the ntpq and ntpdc programs are checked against passwords requested by the programs and entered by hand, so it is generally appropriate to specify these keys in human readable ASCII format.
The optional fourth field is one or more IPs, with each IP separated with a comma. An IP may end with an optional /subnetbits suffix, which limits the acceptance of the key identifier to packets claiming to be from the described IP space.
The ntp-keygen program generates a MD5 symmetric keys file ntpkey_MD5key_hostname.filestamp. Since the file contains private shared keys, it should be visible only to root and distributed by secure means to other subnet hosts. The NTP daemon loads the file ntp.keys, so ntp-keygen installs a soft link from this name to the generated file. Subsequently, similar soft links must be installed by manual or automated means on the other subnet hosts. While this file is not used with the Autokey Version 2 protocol, it is needed to authenticate some remote configuration commands used by the ntpq and ntpdc utilities.
Bugs
It can take quite a while to generate some cryptographic values.